Step by Step Approach to:
Risk Analysis to Risk Reduction
The Function of Risk Analysis for HIPAA Security
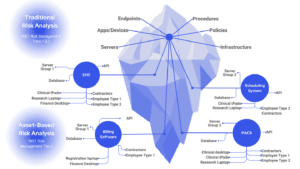
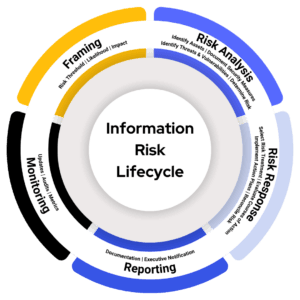
Under the HIPAA Security Rule, a comprehensive risk analysis must be conducted regularly on all systems that create, receive, maintain, or transmit electronic protected health information (ePHI). When new technologies are adopted or significant changes in the operational environment occur the expectations is that a risk analysis is performed as the environments change or new systems and processes are implemented.
These analyses must thoroughly examine how patient data is safeguarded against evolving threats and vulnerabilities, ensuring that the security measures in place are reasonable and appropriate.
Healthcare Cyber Risk Spectrum
Cyber risk reduction is critical as the healthcare landscape has undergone dramatic shifts—a significant concern is vendor or supply chain risk, and the continuous expansion of new services and applications that support enhanced patient care. Telehealth and remote staff was once the focus but now AI is steadily changing the landscape.
This is challenging for risk managment as new cybersecurity threats and vulnerabilities are also on the rise. Unless strategically countered with proven methodologies, these challenges considerably endanger healthcare organizations’ capacity to fulfill their fundamental missions.
In the event of an investigation by the Office for Civil Rights (OCR), organizations must demonstrate that they have not only identified risks to the confidentiality, availability, and integrity of sensitive data but have also implemented reasonable and appropriate security measures and safeguards scaled to the level of identified threats.
Updated: January, 2026
Contents:
What Healthcare Leaders Think about Vulnerability Management…
Vulnerability Management as a Program
Status Quo Can’t Keep Up with Vulnerabiilty Exploitation
Unified Vulnerability Management Program from Clearwater
Reference: Vulnerability Management Requirements Across Compliance Standards…
Ready to get serious about vulnerability exposure risk?
A well-developed cybersecurity risk management program transcends the application of the latest controls or responses to trends like ransomware—it demands a deep understanding of an organization’s unique threats and vulnerabilities so that resources can be allocated wisely to mitigate these risks over time.
OCR looks for demonstrable evidence that an organization’s risk management plan is rigorous and effective, focusing on documented proof that security measures have been integrated appropriately to reduce risk.
Compiling such evidence retrospectively, under the pressure of an OCR inquiry, is a daunting challenge, often leaving organizations with limited time to produce the necessary documentation. Clearwater advocates for a proactive, ongoing risk analysis and response process, ensuring that healthcare organizations can readily demonstrate their commitment to comprehensive cybersecurity risk management.
Define Your Risk Threshold
Do all identified risks require the same priority? The answer involves understanding the nature and magnitude of risks within an organization’s operational landscape.
Although every risk must be documented and continuously monitored, only a specific set of risks must be treated within a given risk cycle—these are risks at or above your risk threshold. As an example, if you rate risk on a spectrum ranging from 1 (Low) to 25 (Critical), a low risk identified as three (3) is not as concerning when compared to a high risk identified as sixteen (16).
Determining your organization’s risk threshold involves understanding two pivotal concepts: your risk appetite and the precision of risk analysis. Crafting a well-defined and accurate risk threshold serves dual purposes: First, it aids in the prudent allocation of cybersecurity investments, and second, it supports the clear definition of acceptable and unacceptable risk levels.
Healthcare organizations, regardless of size, grapple with a multitude of potential security risks that seem to endlessly populate their risk registers, leading to the misconception that every risk demands immediate attention. However, such an approach is not only impractical but also strategically flawed. Effective risk management lies in discerning which threats pose the greatest danger and must receive prioritized attention.
Evaluate Courses of Treatment
After establishing their risk threshold and conducting the risk analysis, organizations have several options to address identified risks: acceptance, avoidance, transfer, and mitigation. Choosing the optimal response hinges on the nature of the risk and its alignment with the organization’s overarching risk management strategy.
Balancing Effectiveness and Feasibility
After outlining possible risk responses, the next critical step toward risk reduction is carefully evaluating the alternatives. The process, well-documented in NIST standards, revolves around two principle considerations: effectiveness and feasibility.
Effectiveness: Prioritizing Impactful Responses
Effectiveness concerns how well the proposed risk response strategy or control achieves the desired outcome in mitigating the risk. The goal is not merely to add more layers of security but to strengthen the resilience of the organization’s defenses meaningfully. Considering the depth and breadth of controls ensures that enhancements contribute genuinely to the organization’s risk posture.
Feasibility: Reasonable & Practical Application
Feasibility is a subjective measurement of how practical and achievable the implementation of a response is, given the organization’s unique constraints and context. For healthcare organizations, any change or introduction of new security measures must be conscientiously weighed against potential disruptions to patient care and clinical operations. It’s crucial to find a balance that maintains security without hindering care delivery.
There was a time when operational convenience might trump security considerations, illustrated by practices such as sharing passwords for ease of access. The healthcare industry, among others, has evolved to recognize the critical importance of securing sensitive information far beyond such rudimentary measures. What once seemed operationally efficient is now considered fundamentally flawed in safeguarding data security and patient privacy.
Holistic Decision-Making
Evaluating risk reduction alternatives demands a holistic approach. Decision makers must balance the scales between the effectiveness of risk response and its feasibility across various dimensions, always optimizing security while maximizing essential clinical workflows. Balancing security and ongoing operations requires a nuanced understanding of the technological landscape and the healthcare environment on which these decisions have the greatest impact.
Managing cybersecurity risks requires a careful evaluation of risk treatment options. Organizations should consider the treatment’s effectiveness in mitigating threats, the associated costs, and its feasibility for implementation.
A treatment’s effectiveness is paramount. Highly effective and impactful treatments (controls) offer strong protection against potential threats and vulnerabilities, while ineffective controls may leave your organization exposed to additional risk or waste resources.
Cost is another factor. Organizations must consider the financial impact of implementing, maintaining, and updating controls. Organizations must strike a balance between effectiveness and affordability.
Finally, the feasibility of risk treatments should be considered. Controls must be reasonably deployed with a manageable level of disruption to existing systems and workflows. In other words, highly feasible controls can be readily integrated.
Clearwater’s IRM|Analysis® software leverages a five-point scale to assess control effectiveness and feasibility. The tool allows organizations to make informed decisions based on their specific needs and constraints.
Evaluating Risk Treatment Options
Once all feasible risk treatment options have been evaluated, the next step is to approve the most effective course of action. During this risk reduction step, it is essential to determine and document a residual risk rating, representing the anticipated risk level present after implementing the chosen controls and risk response strategies. For example, if the initial risk rating is 16 out of 25, business owner(s), information security, and other relevant stakeholders should determine what the risk should be once the proposed controls are implemented. Ultimately, the goal is to bring the residual risk rating within the organization’s risk appetite and below its risk threshold.
Business owners should participate in the decision-making process as they need to be acutely aware of the risks relevant to their respective information systems and business processes. For example, the Director of Health Information Management should be aware of the risks associated with the coding and billing platforms.
Organizations often lack proper communication channels between information technology and business operations, leading to a perception that information risk is solely an IT and Information Security Responsibility. Information risk management is a business function at its core, as the business must provide products and services to its customers, even in the event of technical disruptions. Consequently, the business must participate and take ownership of the risks associated with their respective areas and be actively involved in the risk management process. By ensuring business owners are informed about the risks and are involved in the decision-making process for addressing those risks, organizations can foster a culture of shared responsibility and accountability.
Implementing Risk Response: A Plan for Action
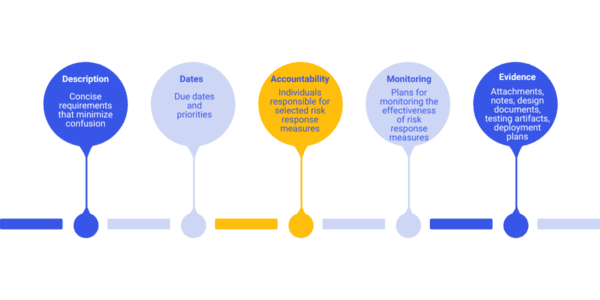
To be successful, risk management requires robust governance. Comprehensive implementation plans are vital and include clearly understood requirements, measurable outcomes, and defined accountability to maximize risk reduction.
As a general rule of thumb, well-documented implementation plans should contain:
- Specific details of controls to be added or enhanced
- Mechanisms for monitoring the effectiveness of the risk response
- Clear timelines and priorities
- Assigned roles and responsibilities
- Risk and issues tracking
Implementation Planning
Example: Untrained Staff
Consider the following risk scenario:
- Threat Source: System Cracker
- Threat Event: Social Engineering
- Vulnerability: Untrained/Untested Staff
To mitigate this risk, we may consider implementing a plan with the following structure:
Risk Owner: Human Resources
Project Manager: John Doe
Open Risks or Issues: Nothing Significant to Report
Priority 1: Improve or update security and awareness training
- Control: Security/Privacy Awareness Training
- Action: Enhance
- Implementation Manager: Information Security & Talent Management
- Due Date: 03/31/2024 (Q1)
Priority 2: Deploy targeted phishing campaigns
- Control: Targeted phishing campaigns
- Action: Deploy
- Implementation Manager: Information Security
- Due: 06/30/2024 (Q2)
Priority 3: Improve audit trail collections and review cadences
- Control: Audit trail collections and cadences
- Action: Enhance
- Implementation Manager: Application Analysts
- Due: 09/30/2024 (Q3)
Priority 4: Validate, refine, and update information disclosure procedures and sanctions policies
- Control: Information disclosure procedures and sanctions policies
- Action: Validate
- Implementation Manager: Legal, Privacy, and Compliance
- Due: 12/31/2024 (Q4)
Organizations can systematically address vulnerabilities over time by treating risk response actions as distinct projects with clearly defined outcomes.
The Final Stage in Risk Reduction: Risk Reconciliation
Following the execution of your risk action plans, risk reconciliation is the final critical step in the risk management lifecycle. It involves a nuanced assessment, often not explicitly detailed in standards but crucial for effective risk management.
After implementing the selected controls, you might expect to reduce the risk to a residual level, say a 9 on a scale from 1 to 25, comfortably below your threshold of 12. However, the unpredictable nature of the implementation process and external factors means the anticipated outcome might not always align with reality. Not all planned controls may be deployed as expected, leading to deviations between projected and actual risk levels.
Risk reconciliation addresses this gap between prediction and reality. It involves revisiting the risk register to update and evaluate the residual risk based on the effectiveness of the implemented controls.
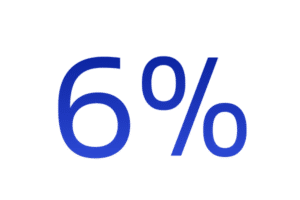
For example, if a risk analyst initially assessed a risk at 16 (on a scale from 1 to 25), predicted it would reduce to 9 after a series of implemented controls, and, upon implementation, verified that the risk should actually decrease to a 6.
Risk Reconciliation supports an accurate, current view of the organization’s risk profile, allowing you to:
- Confirm that implemented controls have effectively reduced the risk to the intended level.
- Adjust your risk management strategies based on the actual outcomes observed.
- Account for changing threats and vulnerabilities
The process of reconciliation is essential for maintaining the integrity and accuracy of your risk management efforts, ensuring that your organization’s risk posture accurately reflects the current state of affairs.
Navigating Your Risk Reduction Journey
As we conclude our exploration from risk analysis to risk reduction, here are pivotal insights to guide your risk management endeavors:
- Respond to All Risks Above Threshold: Every risk warrants a response; acceptance is a strategic choice when aligned with your organization’s risk appetite and overall strategy.
- Diversify Risk Strategies: Beyond mitigation, consider risk avoidance and transfer as potent responses. Remember, avoiding a risk can often be as effective as confronting it directly. Also, consider that risk treatment options can be combined.
- Analysis Over Checklists: Effective risk management is grounded in thorough risk analysis, not merely adhering to checklists or compliance requirements. An in-depth analysis reveals specific threats and vulnerabilities and informs targeted responses.
- Guided Decision Making: Understanding your high-risk scenarios is just the start. Assess multiple treatment options, considering the balance between effectiveness, feasibility, cost, and labor requirements. Let effectiveness, feasibility, and cost principles influence your risk response decisions.
Implementing a disciplined risk management process is a complex but crucial endeavor that requires diligent project management and oversight. Specialized software, like Clearwater’s IRM|Analysis®, can provide structured and automated guidance, enhancing your understanding of risk and facilitating appropriate management action.
Clearwater’s Vulnerability Management Trend Report
View the ups and downs of how healthcare organizations deal with vulnerabilities month by month. Critical vulnerability finding trends show how these contribute to the running risk exposure in healthcare.
This is the only industry specific report for healthcare broken down by market segments. See how your organization compares and the improvement achieved across these segments:
- Healthcare Systems & Surgical Hospitals
- Physician & Medical Specialty Groups
- Healthcare Software and Businesses Associates
Status Quo Can’t Keep Up with Vulnerability Exploitation
Common Vulnerabilities and Exposures (CVE) Growth

Published CVEs rose by roughly 20% from 2024 to 2025, expanding the attack surface and increasing the workload for vulnerability management teams.
This increase reflects broader disclosure participation, expanded CNA coverage, and backlog reductions in scoring pipelines. Counts may vary due to withdrawn CVEs and NVD timing differences.
CVE Numbering Authority (CNA) Growth
CVE Numbering Authorities (CNAs) are approved organizations that assign CVE IDs within defined technology scopes. In 2025, the global CNA community grew by approximately 6%, expanding vulnerability coverage and accelerating disclosure across vendors and platforms.
Known Exploited Vulnerability (KEV) Growth

Known Exploited Vulnerabilities (KEVs) are software and hardware flaws that the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has confirmed are actively being used in real-world attacks. Between 2024 and 2025, the KEV catalog expanded by approximately 20%, underscoring the growing pace of proven exploitation.
Ready to get serious about vulnerability exposure risk?
Clearwater’s Unified Vulnerability Management (UVM) solution is built for the realities of modern healthcare
- IT systems, cloud environments, and connected medical technologies are unified within a single, coordinated vulnerability risk management program.
- Combines continuous IT, cloud, and medical device scanning with 24/7 threat‑intelligence correlation to ensure teams focus on the vulnerabilities that matter most—when they matter most.
- Shifts organizations from raw vulnerability counts to contextualized risk intelligence—prioritizing issues by exploitability, operational impact, and patient safety rather than severity scores alone.
Clearwater’s Unified Vulnerability Management Program
- Directly addresses fragmentation by providing a single, unified inventory and shared operational view across IT, MedTech, and cyber-physical systems
- Enables cross-functional teams to work from the same risk picture
- Clinically informed risk prioritization, we understand healthcare and patient care risk
- 24/7 monitoring and expert guidance, proactively reviewing vulnerability exposure based on emerging threat alerts
- Faster response times and reduced exploit windows with experts assisting with prioritization, rememdiation recomendation or compensating risk mitigating actions
Move beyond fragmented controls toward a more resilient, defensible, and patient-centered security posture with Clearwater Managed Security Services.
Reference
Vulnerability Management Requirements Accross Compliance Standards
Every compliance and regulatory guide for healthcare organizations has a vulnerability management requirement, yet vulnerability risk continues to grow. Here is a recap of the security and compliance frameworks and how they provide guidance for vulnerability management.
Common Requirements Across All Standards and Guidelines:
- Vulnerability identification
- Risk-based prioritization
- Timely remediation or mitigation
- Ongoing monitoring
- Documented governance
HIPAA (Security Rule)
Requirement
Identify, assess, and reduce risks to ePHI.
References
- 45 CFR §164.308(a)(1)(ii)(A) – Risk Analysis
- 45 CFR §164.308(a)(1)(ii)(B) – Risk Management
- 45 CFR §164.308(a)(5)(ii)(B) – Malicious Software
- 45 CFR §164.308(a)(8) – Evaluation
HITECH Act
Requirement
Prevent and reduce breach exposure through reasonable safeguards.
References
- §13402 – Breach Notification
- §13404 – Business Associate Liability
- §13411–13412 – Enforcement & Penalties
CMMC
Requirement
Scan, track, and remediate system vulnerabilities.
References
- RA.1.001 – Identify Vulnerabilities
- RA.2.143 – Scan & Remediate
- RA.3.144 – Risk Analysis
- SI.2.145 – Flaw Remediation
HHS 405(d) (HICP)
Requirement
Healthcare-specific vulnerability management best practices.
References
- Practice #2 – Vulnerability Management
HITRUST CSF
Requirement
Formal, documented vulnerability management program.
References
- 10.1 – Technical Vulnerability Management
- 09.2 – Risk Management
- 01.a – Asset Inventory
SOC 2 (Trust Services Criteria)
Requirement
Identify, monitor, and remediate security vulnerabilities.
References
- CC3.2 – Risk Identification
- CC4.1 – Monitoring
- CC7.1 – Vulnerability Detection
- CC7.2 – Security Monitoring
PCI DSS 4.0
Requirements
- Emphasizes continuous risk assessment and targeted risk analysis rather than only periodic checks.
- Introduces greater flexibility in how requirements are met, but raises evidence and testing expectations.
- Makes explicit the need to define remediation timelines based on risk and to document compensating controls when chosen.
References
- Requirement 6.1 – Identify security vulnerabilities and assign a risk ranking.
- Requirement 6.2 – Ensure systems are protected from known vulnerabilities by installing applicable vendor-supplied security patches in a timely manner.
- Requirement 6.3.1 (PCI DSS 4.0) – Perform targeted risk analysis to determine remediation timelines.
- Requirement 6.4 – Follow change-control processes for system and application changes (includes testing and validation).
- Requirement 11.2.1 – Quarterly internal vulnerability scans.
- Requirement 11.2.2 – Quarterly external vulnerability scans by an Approved Scanning Vendor (ASV).
- Requirement 11.2.3 – Re-scan after remediation to validate fixes.
- Requirement 11.5 – File integrity monitoring (to detect unauthorized changes/exploitation).
- Requirement 12.3.1 – Defined roles and responsibilities for security (supports accountable remediation processes).
