Clearwater CEO Steve Cagle recently chatted with Nilay Patel from Decoder; the two unpacked healthcare security, compliance, and privacy challenges. They gave insight into healthcare outsiders’ perspectives on ransomware and the healthcare industry. Let’s run down some of the highlights of their conversation and other insights around ransomware and the implications for organizations that play a part in the healthcare ecosystem.
Economics
With the value of cryptocurrency plunging, is that slowing down ransomware attacks?
The value of medical data makes ransomware lucrative. Attackers look to healthcare because it’s an industry that has high stakes in the ransom equation. Attackers know this and consider what kind of data they have access to, the exposure implications, and how it may also affect the operations and mission of the healthcare organization. Their ask is customized, so the ransom is explicitly calculated by looking at these economic indicators. Attackers look at organizations and carefully aim for the best price they can feasibly obtain.
If the cryptocurrency mechanism continues, ransomware attacks will continue regardless of the current coin values. The anonymity of transactions allows attackers the freedom to convert digital files and data into immediate digital monetary value when a ransom is paid. Before this point, breached data was stolen and put up for sale on the black market, but this method does not have the immediacy or direct monetary valuation. The attackers have cut out the middleman, which isn’t likely to change.
Isn’t there cyber insurance to help with ransomware economic risks?
There are several ways to deal with risk; mitigation, transfer, avoidance, and allowing for a certain level of acceptance. Other industries like financial and credit card processing account for a certain amount of loss as an acceptable business practice. This is not feasible for healthcare. And avoiding risk is only possible if little change and full control across the entire ecosystem can be obtained, which is not feasible.
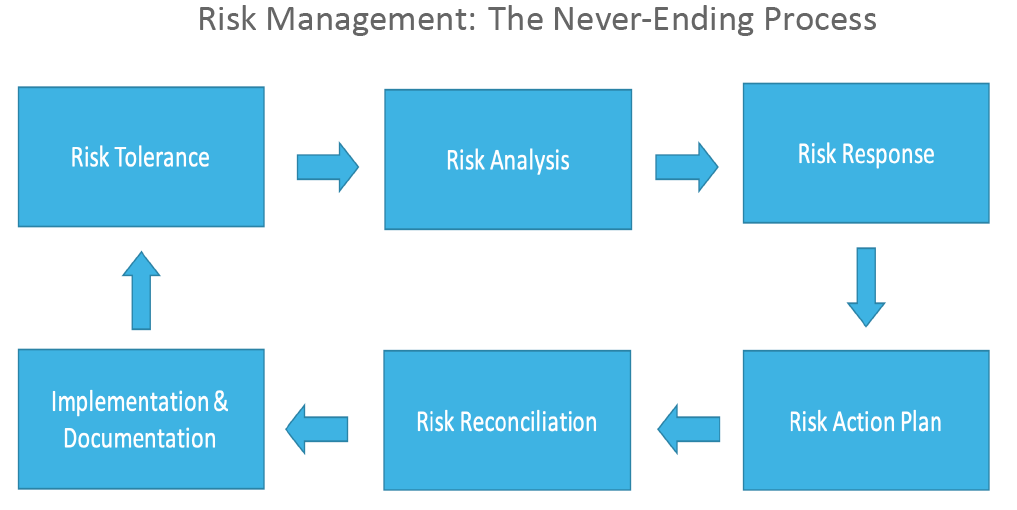
Managing risk is a continuous effort; cybersecurity insurance provides some situational coverage. However, the insurance industry has been burdened with growing cyber claims, leading to mounting losses. It is now much more difficult to match any previous cybersecurity policy coverage without a significant cost increase. Healthcare (and other industries) is dealing with these changes, increasing premiums, higher deductibles, and reduced coverage limits. Even more, restrictions are being carved out, like the potential sub-limits for things like ransomware and Act of War exclusions.
This vehicle provided the transfer of some of the cost of risk to be covered by a cybersecurity insurance policy. Risk ownership never goes away for healthcare covered entities and business associates due to the established Healthcare Security Rule and continuation through HIPAA and HITECH directives. However, cyber insurance now plays a smaller role as executives try to balance risk management and costs.
Ethics
How do you operate and manage during a cyber attack?
The long-standing ethical directive, “do no harm,” and the situational urgency of care put healthcare providers at a disadvantage against their ransomware attackers. If caught unprepared, healthcare organizations may have to make the call to pay the ransom. However, even when paying the ransom, organizations should assume that sensitive data has been exfiltrated even as attackers provide the encryption keys to release their hold. There are cases when attackers have executed double and triple extortion tactics, some contacting the patients directly and threatening data exposure if the individual’s ransom is not paid. Managing ransomware risk should focus on all avenues to mitigate this threat because it’s never as simple as paying or not paying the ransom as some believe.
Attackers also seek the ability to leverage an insider threat, sometimes unwittingly or through coercion. Economic downturn raises the risk of insiders going rogue. This goes both ways, where the attacker community increases and financially stressed insiders with legitimate access to valuable data and IT assets are exposure points. Ethical values may degrade during economic instability adding to the complexity the healthcare industry faces against the risk of ransomware.
Dangerous Assumptions
Is there a problem with healthcare CEOs not investing in cybersecurity?
On the outside, there is a perception that throwing money at this problem is the best route to success. However, the people, process, and technology decisions organizations must make are much more complex. An imbalance in one or more of these three pillars is akin to a three-legged stool that cannot balance. There is a shortage of cybersecurity talent across all industries, making it even harder to fulfill the needs of healthcare organizations. There are over 3,500 security vendors in the market, leading to confusion over what technology mix might be the most effective for their organization. But even with the best security technology and staff, an outdated or broken policy or procedure could provide the means for an attacker to infiltrate or a privacy incident to occur.
The question is not about investing but about adopting continuous risk management and investing in the time for an organization to build out the necessary steps to adjust to current risks, gain insight into trends, and the subsequent controls to improve cyber resiliency.
Isn’t data encrypted everywhere?
Encryption is used at most endpoints, mitigating the chances of a stolen laptop leaking sensitive data. However, healthcare organizations have more diverse systems and environments than any other industry. Rapid changes and growth, accommodating alternative ways to provide care that leverage cloud, IoT, telemedicine, and enhanced patient communication from portals to text require a layered approach to security and privacy controls. There is an oversimplification from the outside of what it takes to support security across the healthcare ecosystem.
Where to Go from Here
Ransomware isn’t slowing down. There is no one action an organization can take to prevent it-it is testing all risk assumptions to date. The earlier threat detection and incident response can occur, the quicker an organization can act before a ransomware event unravels. The latest OCR newsletter focused on incident response, citing increased cyber attacks targeting healthcare sectors.
Clearwater continues to help organizations mitigate their risk and plan for cyber attacks; we’re all working towards a future in which the healthcare industry can safely proceed with a ‘never pay the ransomware’ policy. Enjoy listening to the entire conversation from The Verge’s Decoder Podcast.