By George W. Jackson, Jr., MBA, Ph.D., HCISPP, CISSP, CRISC, PMP
In a time of public crisis where millions of Americans are being asked or forced to stay at home, the opportunity to receive expert medical care through the use of telehealth and remote patient monitoring (RPM) systems offer a promising solution. With the recent passage of legislation permitting healthcare providers to bill Medicare fee-for-service for patient care via telehealth, it is a solution that many providers are now implementing or expanding.
Problems reside in the fact that many mature telehealth implementations and their support staff are being strained to their limits. At the same time, less mature and even relatively new telehealth implementations may be fast-tracked into service ahead of their anticipated schedules without proper testing being completed. These factors, coupled with the fact that cybercriminals are actively seeking innovative ways to take advantage of the COVID-19 crisis, amount to what could be a perfect storm of healthcare cybersecurity risks in the face of a national emergency.
Here I provide an overview of the key components involved in the telehealth/RPM ecosystem and share insight on the security risks that should be considered in deploying solutions.
Care Provider’s Clinical Information Systems
A goal of any telehealth or RPM solution is for clinicians to have access to timely and reliable patient data which can be used to make appropriate clinical decisions. Therefore, at the care provider’s end there will ultimately be an endpoint device that receives and interprets or assists in the interpretation of patient data, meaning there will be issues of security surrounding this endpoint device. For example, in the wake of the current situation, physicians have been given the latitude to use personal devices to perform telehealth communications. The use of personal devices increases an organization’s vulnerability to an attack. The likelihood of a successful attack increases if the devices are unmanaged by the organization’s IT and information security resources and lack appropriate security controls.
Furthermore, telehealth systems are typically connected to the healthcare system’s network which involves routers, switches, firewalls, Ethernet, Wi-Fi, VPN, and most likely, depending on the size of the organization, a data center or multiple data centers, with physical and virtual servers, storage systems, and a host of other applications and devices. Because all of these system components are interconnected, a vulnerability due to a deficiency in security controls in one area can have ripple effects across the entire information technology ecosystem. Therefore, a breach in one area, such as a denial of service attack or even a ransomware attack, could have serious repercussions on an unrelated system, such as a telehealth system, which has increased from occasional use to 24×7 operation and is now unavailable.
Vendor Information Systems
Telehealth relies upon a variety of devices, software applications, and communications technologies to connect from a remote location back to a healthcare provider’s office. In most cases, these complex communication systems require the services of vendors or suppliers who may also engage their own vendors and suppliers to deliver their solutions. This complex, multi-stakeholder environment increases the potential attack surface for malicious actors seeking to compromise a telehealth system. The goal is to uncover a security flaw that allows the attacker to either gain access to electronic protected health information (PHI) that is created, received, maintained, or transmitted through the system or to compromise the availability of the system.
Ensuring that vendors and all related third parties have and maintain a sound security posture is critical to the health and welfare of these systems and likewise to the health and welfare of the patient. Otherwise, vulnerabilities such as exposure to insecure public and private networks via the cloud, insufficient application security, network access controls, system patching, or data integrity monitoring and inadequate security incident response can provide cyber criminals with a staging area that can be used to launch cyberattacks against the host system and other systems that are interconnected.
The Patient Home Environment
While not as complex as securing the care providers’, vendors’, or telehealth and RPM systems’ environments, the patient’s home information technology environment is becoming more diverse each day. Key components of the patient’s home technology environment include personal firewalls, cable modems, wireless routers and access points, PCs, laptops, tablets, smartphones, and smart home devices (such as home security systems or appliances) sitting on the patient’s home network.
In addition to those components, for telehealth applications, there may also be patient monitoring equipment deployed in the home to perform diagnostic tasks (e.g., blood pressure, glucose levels, BMI/weight measurement) or provide key data to continuous patient monitoring systems (such as cardiac implanted electrical device monitoring systems) designed to transmit information and alerts about the health of the device as well as the health of the patient. While these devices, in and of themselves, may be more or less sound, vulnerabilities may exist in the user’s home environment, such as lack of cybersecurity awareness, lack of adequate password security, lack of data encryption, and inadequate use of two-factor or multi-factor authentication. These vulnerabilities provide a skillful and enterprising cybercriminal the opportunity to exploit a known or even a zero day vulnerability on a piece of patient monitoring equipment in the hope that this vulnerability can be used to access critical backend systems of a supplier or possibly even a healthcare provider.
The Need for Increased Cyber Vigilance and Cyber Resilience through Implementation of the NIST Cybersecurity Framework
Now more than ever, expert application of the NIST Cybersecurity Framework can assist organizations and patients in maintaining, and even ramping up, their cyber vigilance and cyber resilience in the face of threats brought on by the need to rapidly deploy and expand telehealth and RPM. Below is a brief re-cap of the core elements of the NIST Cybersecurity Framework and how they may be applied to telehealth and RPM.
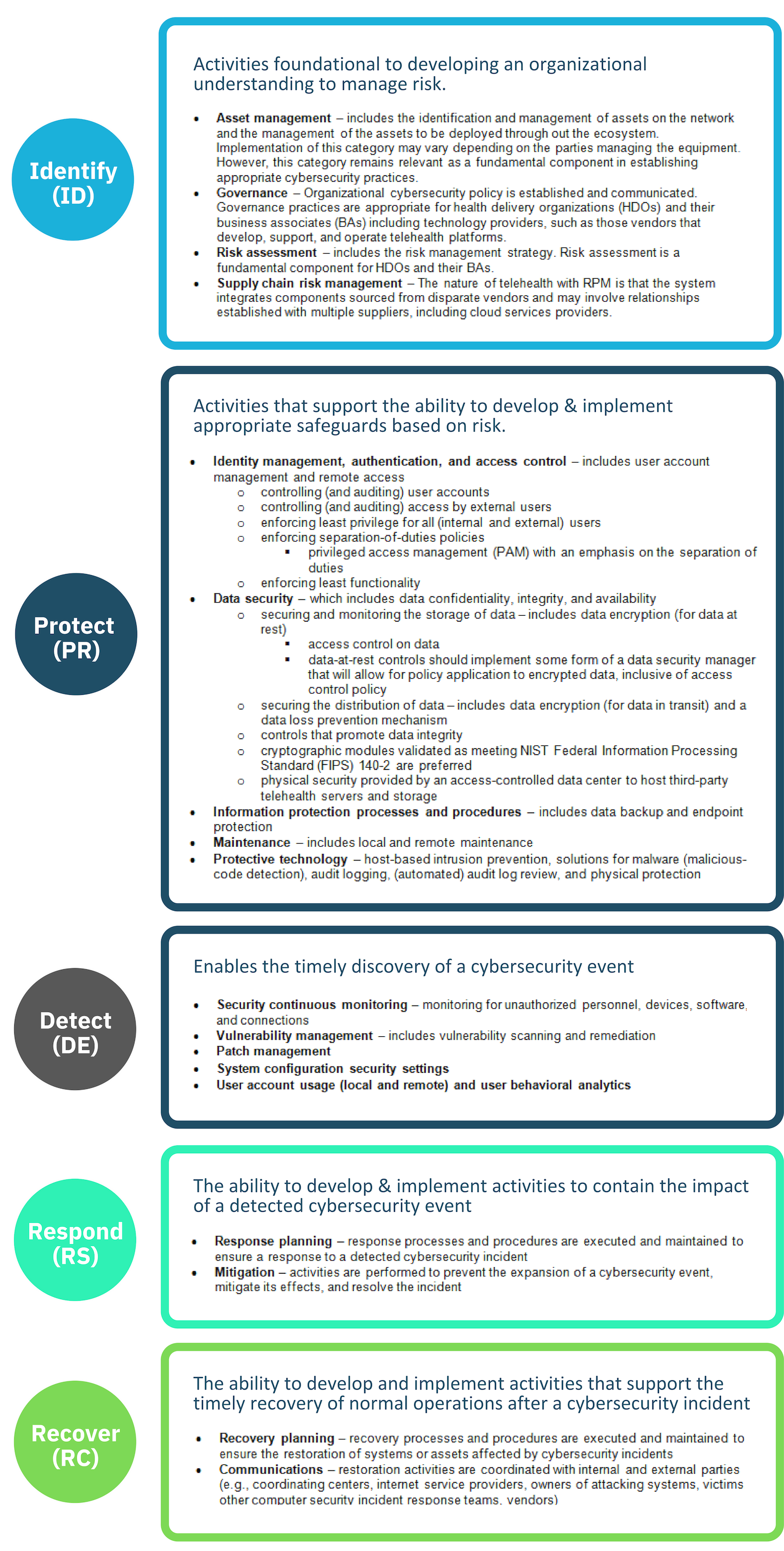
Table adapted from “Securing Telehealth Remote Patient Monitoring Ecosystem: Cybersecurity for the Healthcare Sector.”
At Clearwater, we are experts at implementing the NIST Cybersecurity Framework, and we have done so successfully for numerous healthcare organizations over the years. If you have any questions or would like to discuss plans to implement the NIST Cybersecurity Framework in a current or planned telehealth/RPM solution, we would be happy to talk with you about it today.
Contact your representative or reach out to us at info@clearwatercompliance.com.